What is MeshaSec?
Autonomous Application Security Testing for the modern web.
The Problem with Traditional DAST
Legacy DAST tools were built for the static web of the 2010s. They struggle with modern Single Page Applications (SPAs), complex authentication flows (MFA/TOTP), and the dynamic state nature of React, Vue, and Angular apps. Standard crawlers often fail at the identity gate, leaving up to 70% of your most sensitive surfaces in the shadow. The result is a false sense of security and a deluge of false-positive probability scores.
Manual Zero-Config Wizard
MeshaSec eliminates the need for complex YAML configurations, brittle manual proxy recording, or security expertise. Our **Scan Setup Wizard** allows you to define your target, scope, and authentication in seconds. By automating the "human intent" of a security researcher, we move from manual testing to autonomous orchestration.
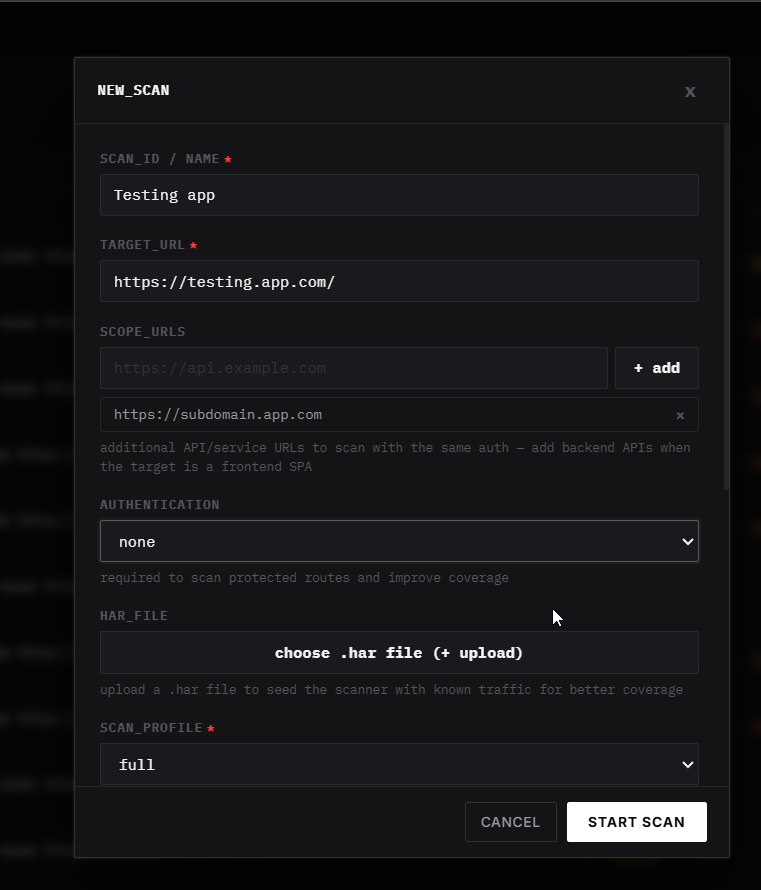
Method A: Precise manual control via the New Scan Wizard.
Conversational Orchestration
For security teams that value speed and developer experience, MeshaSec offers a conversational alternative. Simply instruct the **AI Node** via a natural language command to initiate a scan. The engine will handle target discovery, identity handshakes, and scoped audits autonomously.
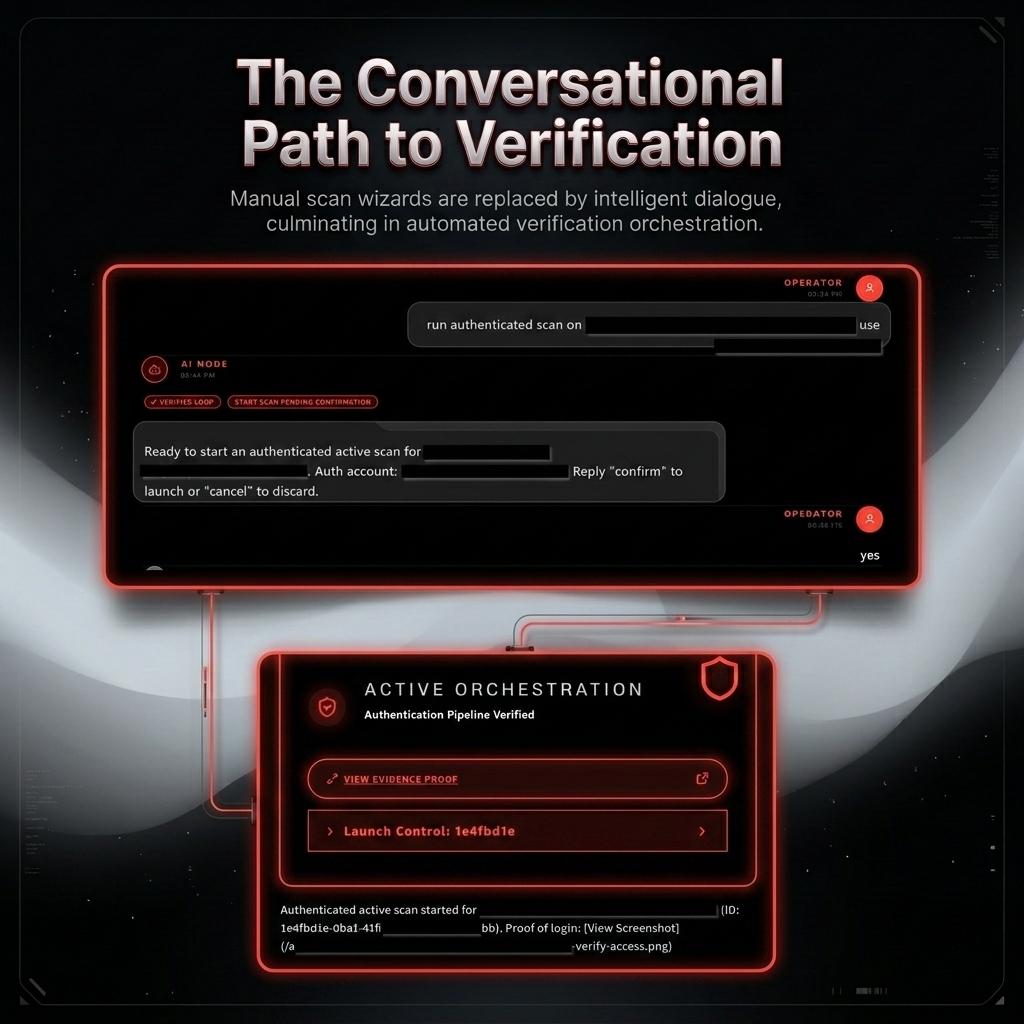
Method B: Conversational intent mapping to verified authenticated scans.
The MeshaSec Difference
MeshaSec introduces **Autonomous Discovery Nodes**. Instead of simple link crawling, our engine understands the application's state machine. We navigate through identity boundaries and complex UI state transitions as a real user would, delivering deterministic proof-based findings instead of probability scores.
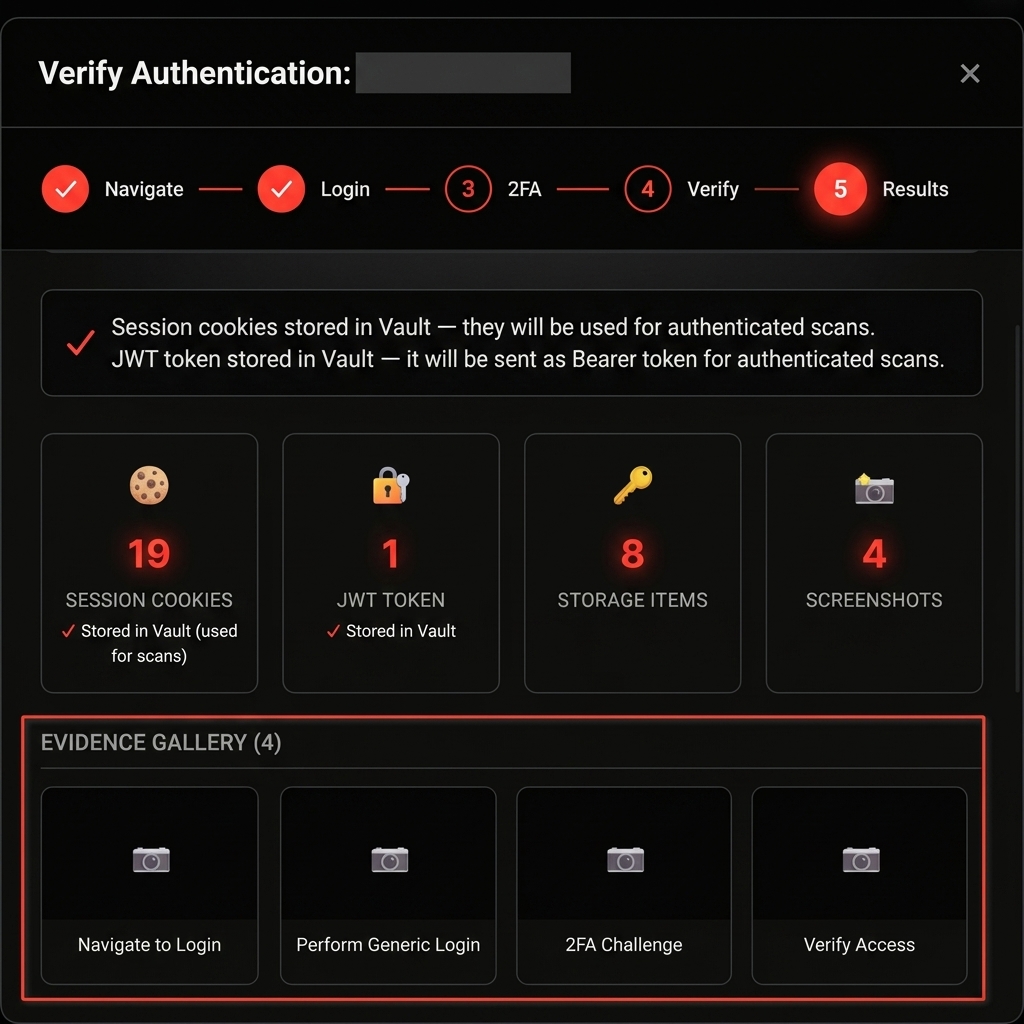
Protocol Truth: MeshaSec captures real-time session state, JWT tokens, and browser storage as irrefutable proof of access.
Core Philosophy
We believe security intelligence should be **autonomous**, **conversational**, and **deterministic**. By automating the "human intent" of a security researcher, we provide 99.9% noise reduction and irrefutable protocol truth. Our goal is to turn DAST from a "scanner" into a "verification engine."